至少是名字先起好了。
与极客交朋友
极客是一群社交能力比较弱的人,同时他们又是不甘心于任何不足、缺陷的人,所以他们靠算法搞定社交,整出各种社交网站和应用来颠覆你们这些社交能力强的人的世界。现在你们完了,以前你们玩什么都不带上极客,不光爱理不理的,甚至常常有嘲笑、愚弄极客们的现象,可如今你们的世界已经被极客们征服,你们的社交已经完全离不开极客们创造的工具,你们不得不开始膜拜极客们,你们需要学习如何跟极客交朋友。
极客分两类,一类由geek这个单词的本意演变而来,一类由极客精神引申而来。
第一类描述的人群比较窄,geek本来的意思是不寻常的、古怪的人,通常是令人讨厌的,以前当人们说一个人很geeky的时候是带着鄙夷的,类似于中国人常说的书呆子。可是随着这些呆子们用facebook、twitter、foursquare、instagram、line、vine、path、tesla等等一次次地对这个世界做出改变的时候,这个单词的释义慢慢由贬义转向褒义了,出现了电脑高手、技术高手、追求极致等等的意思。这类极客总体上还是跟技术,尤其是计算机技术相关的,所以人群还比较小。
第二类就是在极客们的那种不甘于平庸、不完美而追求极致,用行动对这个世界做出改变的精神气质上扩展开来的人群。这样极客这个称号就不仅仅被限制在技术方面了,如果你是个烹饪高手,不断做出创新你就是极客;如果你是个艺术家,用不同于寻常的方式创作你也是极客;即使你仅仅是在街上摆摊的,但你用了独到的方式来经营你的小买卖进而引起了轰动,你同样是个极客。这样极客的人群就扩大到了各行各业了,极客就是在各个领域里的那一批人,他们不满足于现状,不断发现周围世界的不足然后用极致的方式进行改造。
极客所涵盖的人群再广也改变不了他们是小众的事实,因为大众之所以是大众就是因为他们只希望能享受少数人努力带来的改变。而人的本性就是懒惰的,极客们就是被选中的那少数能克服懒惰,比大众多迈出了一步的人——他们不仅仅是想到这个世界应当要有什么改变,而且会付诸行动亲手来进行改造。
了解了极客才有可能跟他们交朋友。
- 极客们很专注,因此不希望被打扰,所以不要拿无聊的琐事去烦他们,他们不会鸟你;
- 不要去忽悠他们,因为他们的智商通常都很高,你忽悠他们的时候他们只是为了不伤你的面子不给你点破而已;
- 发自内心地尊重他们,因为有了他们我们的世界才变得越来越用户友好,你仅仅是支付了钱是无法跟他们所做出的改变背后的意义相提并论的;
- 极客们不喜欢说太多,只喜欢做更多,他们这样要求自己,也同样要求自己的朋友,你想做他们的朋友就尽量用行动来表示,他们对只有言语而没有实质行动的现象都会在自己的社交公式里给化掉的,在他们眼里不存在;
- 极客们很注意谈话与思考的逻辑,他们倾向于只给你逻辑清晰地描绘一次他们的想法就够了,如果你不能很快明白,他们会找各种借口来远离你;
- 极客们不太懂得站在别人的立场考虑问题(主要是不愿意),在他们眼中你就是一个黑匣子,跟他们交流只需要提供几个API接口进行高效的信息置换就可以,他们才懒得管你内部如何处理呢,他们认为那是你自己应当搞定的事……
其实最好的一种方式,就是你也成为一个极客,不仅仅幻想这个世界应当有什么改进的地方,更是拿出行动来改造这个世界,你就能真正理解极客并且成为极客们的好朋友了。
你的烦恼源自雷锋
记得小时候我就被洗脑,要“爱憎分明”,成天唱着要学习雷锋的歌曲。当然了,他们的目的是把红色的思想灌输给我们这些娃娃们,我这会儿想探讨的不是这个,而是这个灌输产生的一个副作用——把人与人的情感划分成不同种类之后而产生的危害。
人们是怎样做到“爱憎分明”的呢?我们其实把这个情感分得非常细,表达爱的词汇就有诸如喜爱、热爱、爱慕、爱恋、迷恋、关爱、敬爱、爱护等等,表达憎的词汇也有诸如讨厌、厌恶、鄙视、憎恶、憎恨、仇恨、恨之入骨、势不两立、你死我活……。我原本想由爱到恨按程度深浅把这些词汇给排个序的,结果发现工程浩大,最初的这个冲动立马被击倒了。想象一道彩虹,它表现出来的其实是由红到蓝的光谱,把那些词语按照由爱到憎排列形成的光谱可能要比彩虹宽出不知道多少倍。
由爱到憎的感情如此之多并且如此细腻,以致于人们无法轻易掌握和管理,于是人们就把这些感情与所相关的对象建立关联,就可以方便地处理了。比如人们把周围的人划分为父母、子女、情人、朋友、配偶、兄弟姐妹、亲戚、同事、陌生人、公敌(媒体宣传造就的坏人)、死敌等角色,对待这些不同的对象的时候,就可以像换档一样,直接把情感切换到相应的档位上,用相应的情感处置即可。
人们早就活得跟机器人一样了,只是自己不知道。
比如走在大街上,人们都对陌生人尽可能地回避彼此的目光,一般都是漠视,偶尔目光相接了会飞速的转到别处,甚至还会瞪对方一下,好像在说“看什么看,流氓!”。同样一个人,由朋友带来,立刻换档,即使还没认识,也会变得亲切了许多,目光相接后也会微笑一下。
又比如同事与朋友这两个档,当我们把一个人定位为普通同事的时候,即使对方对你再好, 永远都会隔着一些东西;而面对朋友就立刻换档,即使对方骂你,发自内心地嫌你烦,你也会敞开心扉地倾诉。
死敌与朋友也非常有意思,大脑换成“死敌”档的时候,对方所有优点完全消失,任何善意的努力都是别有用心。而如果发生了什么事让大脑换档了,切换到“朋友”档,对方的所有一切令人产生的情感都是正面的,看到问题也会主动包容,于是就发生了“化敌为友”的戏剧化的一幕。
佛经中提到类似的划分的时候分得很粗,就是我、人、众生,并且分析了有这些分别心之后人们是如何变得愚痴,进而产生各种烦恼的。可是现在看来我们人类的愚痴何止于此啊!
我一直以来要求我自己,把这个世界简化,在我与人之间只有一个情感,不去用某一个具体的词汇给它标注,用最大化的真诚面对每一个人。我对待上述人为划分的不同角色的时候采用一样平等的对待,因此我的父母觉得我叛逆,但同时觉得我独立,有问题会以朋友的姿态来探讨;我的朋友们可以不用经常联系,不用刻意维护,虽然见面常常埋怨几句,可是仍然亲切无比;有过误会把我当过敌人的,用真诚化解之后仍然如朋友一般毫无障碍……
当然我还会遇到很多的烦恼,甚至偶尔还会有着急发火的时候,我知道那是因为我没有简化彻底,还有我相与人相的分别,但即使仅仅做到这样,我对于仍然时不时产生的烦恼也能很轻松、坦然地面对,能够沉着地思考最优的解决方案,尽可能保证我的着急发火不至于产生无法挽回的坏影响。
我真心希望人们都能享受同样的快乐,而这个方法就是不要划分界线,忘掉描绘情感的那些词语,忘掉隔在你对面那个人与你之间的那个标签,不论对方是谁,都以诚相待,平等相待,在人与人相处方面“爱憎不分”,你就会拥有一个更加幸福的人生。
另:标题仅仅是开个玩笑罢了,你的烦恼与雷锋同志无关,别把责任推到他老人家身上。
我会飞,可我更要很爽地飞——写在2014年第一个工作日
我是从大概十几年前开始会飞的。
可惜的是,在过去的这十来年里,我并不能总是像电视里的超人那样很爽地飞。是这样的,在起飞之前我心里会产生一个意念——要飞了。一般情况下,我可以通过这个意念反馈来的感觉来判断接下来的飞行状态可能是什么样的。当我判断出当前处在能飞的状态下的时候,下一步我一般会先轻轻跳起来——如果这时候是站在高处会让后面的步骤更轻松一些,跳到最高点的时候我会把身体向前倾,尽可能保持面朝下、身体与地面平行,如果要往高处飞的话当然头部要翘起来一些。接下来,我要在身体开始下落前把手向前伸去(伸一只或两只都可以)。如果状态好的话,我就直接可以向前飞出去了。但大多数时候不会那么爽,由于我游泳的时候习惯蛙泳,而在游泳的时候会有那么一丁点像飞的感觉,因此大多数时候我在飞得不太爽的时候,不由自主地会用蛙泳的动作来辅助飞行,也就是先用双腿往后蹬,如果再差一点儿,还得加上胳膊的动作。总之,这是我大多数情况下飞行的步骤。在飞得不爽的状态下,我通常只能维持在一棵树的高度,有时甚至会更低。所以,虽然这样飞比走路好多了,但总是不太爽。
偶尔在起飞前,意念反馈过来明显感觉状态极佳。这种情况那可就爽呆了,没有那么复杂的动作,只要把手伸出来,随意起飞,指哪儿飞哪儿。这种飞行是非常爽的。不像黑客帝国里的Neo,还要下蹲蓄势一下,把地面都压变形了,然后才能飞起来。我就直接飞走了。真想每次都有这样的飞行状态。
其实在最初的时候,我大多数情况下都是那种很爽的飞行状态。刚开始能飞到大厦顶上,后来又能飞到山顶上,再后来能飞到云层的高度,接着飞到了月亮上,最夸张的一次,我飞过了九重天,摸到了最后一重天,在我打算要从一个洞钻上去的时候,不知道为什么被一股力量压下来了。我当时能隐约听到那一重天上面的人声,很可惜没能混上去开开眼。自那以后就再也没有过那样的机会了。
那种爽的状态也就持续了两三年左右。后来大多数时间里,我好像被地面给牵制住了,常常要费很大力气才能飞到树的高度,之后就再也很难上升了。即使是我能飞到常年积雪的山顶上,也是一直与山坡保持着一棵树的高度那样飞上去的,到了山顶,也无法飞更高。
这些年我为这一点常常感到迷惑,到底是发生了什么事呢?为什么飞不起来了?
也搞不清楚为什么,在过去的一、两年中,我隐隐约约地感觉到我的飞行状态在好转,能飞到云层高度的次数多了起来,也常常在城市的摩天大厦顶部穿梭。更牛的是,我不仅仅能在空间里穿梭,偶尔还会在时间里穿梭,有时候还会在不同的维度间穿梭,常常飞到不知道什么星球上去。
我隐约觉得我快要突破一些什么了。如果突破了会是什么样的状态呢?自由自在地穿越时空,在不同维度的世界里来去自如?真心期待啊。
这个突破是要发生在2014年吗?耶!努力,加油!
借学英语来谈谈我对学习的看法
我们外语教学中最普遍的误区就是认为:英语=单词+语法+发音。因此产生了大量的神棍式的单词、语法、发音专家,去片面甚至是畸形地吹嘘各种大法来忽悠学习者,把非常简单的一件事情给变得无比复杂。
老师没学好,不仅用错误的方法继续误导下一代,有些心胸不够开阔的还用各种手段阻止学生用正确的方法学习。
如果达尔文的假设是正确的,那么从原始人到现代人沟通方式是这样进化的:叫喊→口语→文字→规则(语法、语音等)→互联网。由此可见,我们主流的英语学习方法是本末倒置的,能学好语言才怪呢。这也是为什么某教采用最原始的形式——“叫喊”——反而比学校的方法要好一些。
从进化的角度来说,你我都处在人类进化的最前沿。我们的生理条件是历史上各种“家”都不具备的;从当下来看,人一生对自己的大脑的开发程度只有很少一部分。由此可见,我们的潜力是无穷的,什么孔子、老子、孙子,什么牛顿、爱因斯坦,你都完全能比他们更厉害,唯一的障碍就是你自己停滞不前。
“刻苦”这个词是个害人精。我们的教育不断给学生灌输学习的恐怖故事:书山有路勤为径,学海无涯“苦”作舟、头悬梁、锥刺骨、在墙上打洞、到雪地里读书……把学习如此扭曲对你们有什么好处呢?我个人的经验表明,学习一点都不苦!如果觉得苦了请一定记住,你那不叫学习,赶紧STOP!
让我告诉你关于学习的最大的秘密:学习 = 玩。当你感觉自己在学习的时候,并不是最佳的学习;当你感觉自己在玩的时候,那才是真正的最佳学习状态。
如果想让太阳光照到本来照不到的墙面上,我们可以在阳光照得到的地方拿面镜子来反射阳光。但我们能一下就将阳光反射到自己想要的地方吗?如果够幸运,可以(或者常玩这个,技术高超也行)。其它情况下我们就得慢慢调整角度了。在不断调整的过程中,我们开心地玩着,享受这个不断改错的过程。
学好语言的第一步就是爱上语言。因为如果你不爱却非要学,会有以下三大危害:1. 自己很难学好;2. 将来再想学的时候更难学好;3. 学不好不由得你就会散布语言很难学、单词不好记、发音很重要等谣言,害得别人也学不好。
工欲善其事,必先利其器。一个最适合你自己的语言能力获得环境不容易找到,但你可以自己创造。比如我在中学的时候就会随身带着这些:随身听、收音机、小笔记本、笔、电子词典、杂志……我的目标是无论身在何处,都有一个完全浸泡在目标语言中的环境。
人的一生就是一个学习的过程。只要我们永远保持纯净的心灵,不要带偏见,以一颗真诚的心看待任何事物,我们都会有收获。不要停滞不前。如果能永生,即使学得最慢的人最终也会成为圣人。但从现实来看好像我们都不能永生,所以在有限的时间里,尽可能去学习更多的东西,让我们不枉来此世界一趟。
学习时间是自己一点点地挤出来的,如果大块的时间很少的话就利用好零碎时间,养成习惯就好了。我走到哪儿第一件考虑的事就是要带本什么书,这样在路上或者任何在不知不觉中浪费掉的时间都会被我用来学习,并且这样学习的效果其实也特别好。
一个人在下决心做一件事的时候刚开始都很有冲劲,一旦停下来一段时间就会开始自责,骂自己又没有坚持,很多负面的情绪就都来了。其实这个时候是很关键的,要是能马上原谅自己,就不会再去浪费时间想这个问题了。所以要告诉自己:这没什么大不了的,只是暂停了一下而已,我现在就要接着去做!
中本聪(Satoshi Nakamoto)关于比特币的那篇论文
今天上午在BTCChina上比特币一度涨到了2600多,一个多月前抱着试试看的心态,充了2500块钱开始玩,那时候才六百多一个比特币,虽然有点遗憾当初没多买点,但是也要保持理性,上午在2500的时候卖出一个之后把2500块钱提现。用帐户余额继续玩。这样即使将来亏完了,于我实际也没有什么影响,我的2500反正已经收回来了。
听说比特币多半年的时间了,但还没真正专心钻研过,所以先把这个发明的源头找到,一点点学习。搜到了比特币的发明者中本聪(Satoshi Nakamoto)的那篇论文,要是能弄明白,有空闲的话我试试看能不能把这篇论文给翻译一下。
Bitcoin: A Peer-to-Peer Electronic Cash System
Satoshi Nakamoto
[email protected]
www.bitcoin.org
Abstract. A purely peer-to-peer version of electronic cash would allow online payments to be sent directly from one party to another without going through a financial institution. Digital signatures provide part of the solution, but the main benefits are lost if a trusted third party is still required to prevent double-spending. We propose a solution to the double-spending problem using a peer-to-peer network. The network timestamps transactions by hashing them into an ongoing chain of hash-based proof-of-work, forming a record that cannot be changed without redoing the proof-of-work. The longest chain not only serves as proof of the sequence of events witnessed, but proof that it came from the largest pool of CPU power. As long as a majority of CPU power is controlled by nodes that are not cooperating to attack the network, they’ll generate the longest chain and outpace attackers. The network itself requires minimal structure. Messages are broadcast on a best effort basis, and nodes can leave and rejoin the network at will, accepting the longest proof-of-work chain as proof of what happened while they were gone.1. Introduction
Commerce on the Internet has come to rely almost exclusively on financial institutions serving as trusted third parties to process electronic payments. While the system works well enough for most transactions, it still suffers from the inherent weaknesses of the trust based model. Completely non-reversible transactions are not really possible, since financial institutions cannot avoid mediating disputes. The cost of mediation increases transaction costs, limiting the minimum practical transaction size and cutting off the possibility for small casual transactions, and there is a broader cost in the loss of ability to make non-reversible payments for non- reversible services. With the possibility of reversal, the need for trust spreads. Merchants must be wary of their customers, hassling them for more information than they would otherwise need. A certain percentage of fraud is accepted as unavoidable. These costs and payment uncertainties can be avoided in person by using physical currency, but no mechanism exists to make payments over a communications channel without a trusted party.
What is needed is an electronic payment system based on cryptographic proof instead of trust, allowing any two willing parties to transact directly with each other without the need for a trusted third party. Transactions that are computationally impractical to reverse would protect sellers from fraud, and routine escrow mechanisms could easily be implemented to protect buyers. In this paper, we propose a solution to the double-spending problem using a peer-to-peer distributed timestamp server to generate computational proof of the chronological order of transactions. The system is secure as long as honest nodes collectively control more CPU power than any cooperating group of attacker nodes.2. Transactions
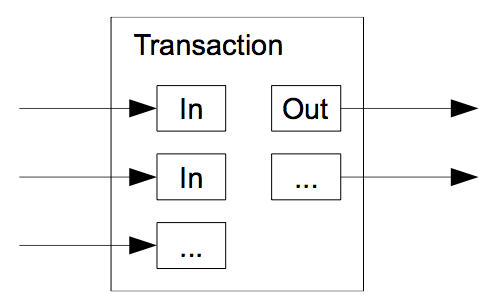
We define an electronic coin as a chain of digital signatures. Each owner transfers the coin to the next by digitally signing a hash of the previous transaction and the public key of the next owner and adding these to the end of the coin. A payee can verify the signatures to verify the chain of ownership.
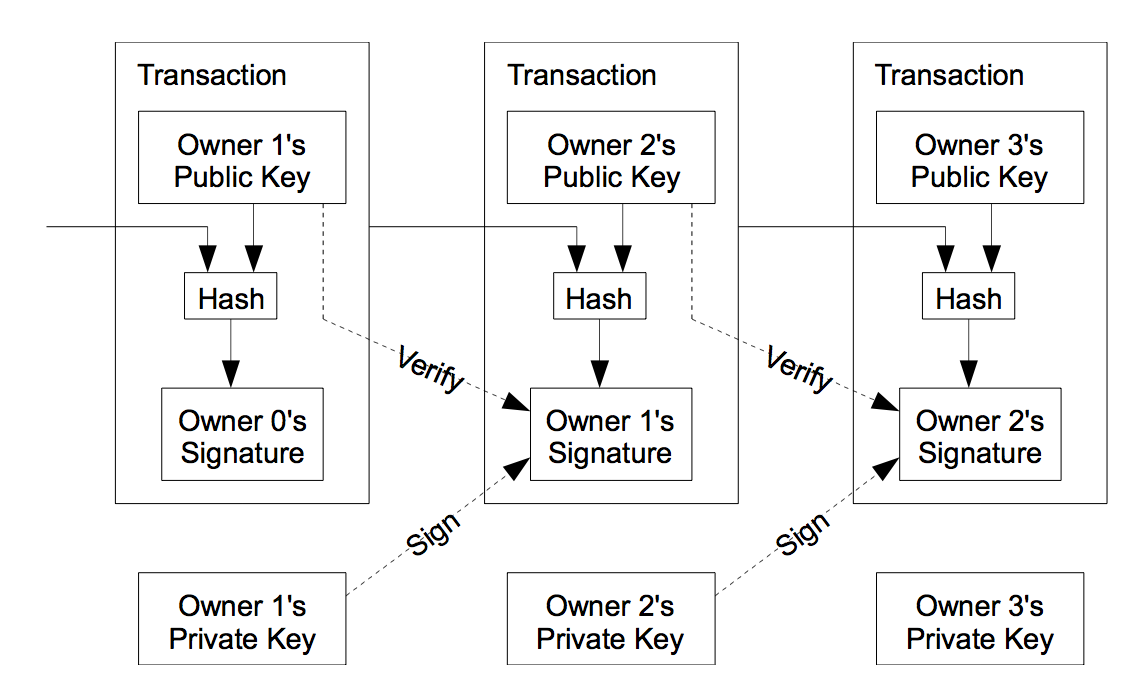
The problem of course is the payee can’t verify that one of the owners did not double-spend the coin. A common solution is to introduce a trusted central authority, or mint, that checks every transaction for double spending. After each transaction, the coin must be returned to the mint to issue a new coin, and only coins issued directly from the mint are trusted not to be double-spent. The problem with this solution is that the fate of the entire money system depends on the company running the mint, with every transaction having to go through them, just like a bank.
We need a way for the payee to know that the previous owners did not sign any earlier transactions. For our purposes, the earliest transaction is the one that counts, so we don’t care about later attempts to double-spend. The only way to confirm the absence of a transaction is to be aware of all transactions. In the mint based model, the mint was aware of all transactions and decided which arrived first. To accomplish this without a trusted party, transactions must be publicly announced [1], and we need a system for participants to agree on a single history of the order in which they were received. The payee needs proof that at the time of each transaction, the majority of nodes agreed it was the first received.3. Timestamp Server
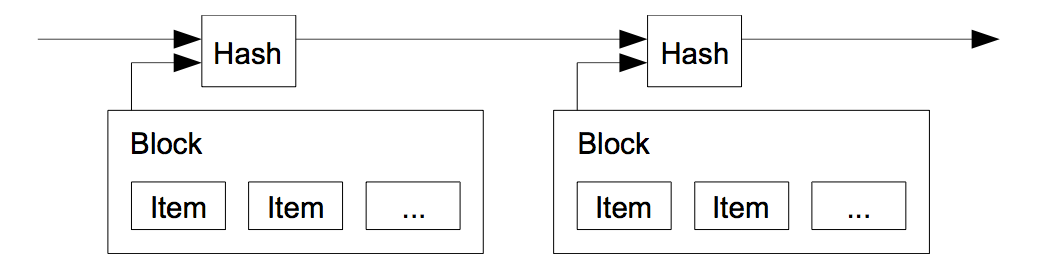
The solution we propose begins with a timestamp server. A timestamp server works by taking a hash of a block of items to be timestamped and widely publishing the hash, such as in a newspaper or Usenet post [2-5]. The timestamp proves that the data must have existed at the time, obviously, in order to get into the hash. Each timestamp includes the previous timestamp in its hash, forming a chain, with each additional timestamp reinforcing the ones before it.
4. Proof-of-Work
To implement a distributed timestamp server on a peer-to-peer basis, we will need to use a proof- of-work system similar to Adam Back’s Hashcash [6], rather than newspaper or Usenet posts. The proof-of-work involves scanning for a value that when hashed, such as with SHA-256, the hash begins with a number of zero bits. The average work required is exponential in the number of zero bits required and can be verified by executing a single hash.
For our timestamp network, we implement the proof-of-work by incrementing a nonce in the block until a value is found that gives the block’s hash the required zero bits. Once the CPU effort has been expended to make it satisfy the proof-of-work, the block cannot be changed without redoing the work. As later blocks are chained after it, the work to change the block would include redoing all the blocks after it.
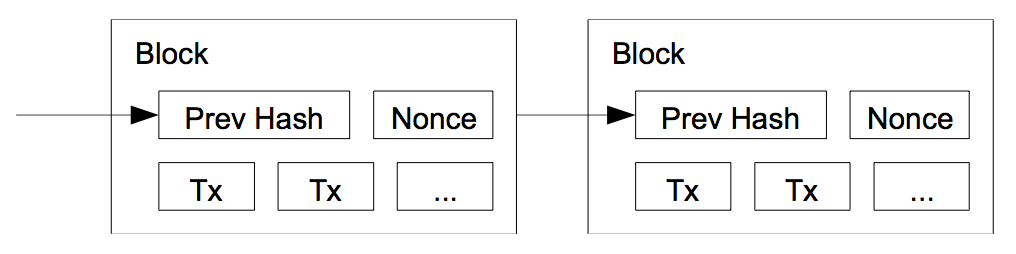
The proof-of-work also solves the problem of determining representation in majority decision making. If the majority were based on one-IP-address-one-vote, it could be subverted by anyone able to allocate many IPs. Proof-of-work is essentially one-CPU-one-vote. The majority decision is represented by the longest chain, which has the greatest proof-of-work effort invested in it. If a majority of CPU power is controlled by honest nodes, the honest chain will grow the fastest and outpace any competing chains. To modify a past block, an attacker would have to redo the proof-of-work of the block and all blocks after it and then catch up with and surpass the work of the honest nodes. We will show later that the probability of a slower attacker catching up diminishes exponentially as subsequent blocks are added.
To compensate for increasing hardware speed and varying interest in running nodes over time, the proof-of-work difficulty is determined by a moving average targeting an average number of blocks per hour. If they’re generated too fast, the difficulty increases.5. Network
The steps to run the network are as follows:
- New transactions are broadcast to all nodes.
- Each node collects new transactions into a block.
- Each node works on finding a difficult proof-of-work for its block.
- When a node finds a proof-of-work, it broadcasts the block to all nodes.
- Nodes accept the block only if all transactions in it are valid and not already spent.
- Nodes express their acceptance of the block by working on creating the next block in the chain, using the hash of the accepted block as the previous hash.
Nodes always consider the longest chain to be the correct one and will keep working on extending it. If two nodes broadcast different versions of the next block simultaneously, some nodes may receive one or the other first. In that case, they work on the first one they received, but save the other branch in case it becomes longer. The tie will be broken when the next proof- of-work is found and one branch becomes longer; the nodes that were working on the other branch will then switch to the longer one.
New transaction broadcasts do not necessarily need to reach all nodes. As long as they reach many nodes, they will get into a block before long. Block broadcasts are also tolerant of dropped messages. If a node does not receive a block, it will request it when it receives the next block and realizes it missed one.6. Incentive
By convention, the first transaction in a block is a special transaction that starts a new coin owned by the creator of the block. This adds an incentive for nodes to support the network, and provides a way to initially distribute coins into circulation, since there is no central authority to issue them. The steady addition of a constant of amount of new coins is analogous to gold miners expending resources to add gold to circulation. In our case, it is CPU time and electricity that is expended.
The incentive can also be funded with transaction fees. If the output value of a transaction is less than its input value, the difference is a transaction fee that is added to the incentive value of the block containing the transaction. Once a predetermined number of coins have entered circulation, the incentive can transition entirely to transaction fees and be completely inflation free.
The incentive may help encourage nodes to stay honest. If a greedy attacker is able to assemble more CPU power than all the honest nodes, he would have to choose between using it to defraud people by stealing back his payments, or using it to generate new coins. He ought to find it more profitable to play by the rules, such rules that favour him with more new coins than everyone else combined, than to undermine the system and the validity of his own wealth.7. Reclaiming Disk Space
Once the latest transaction in a coin is buried under enough blocks, the spent transactions before it can be discarded to save disk space. To facilitate this without breaking the block’s hash, transactions are hashed in a Merkle Tree [7][2][5], with only the root included in the block’s hash. Old blocks can then be compacted by stubbing off branches of the tree. The interior hashes do not need to be stored.
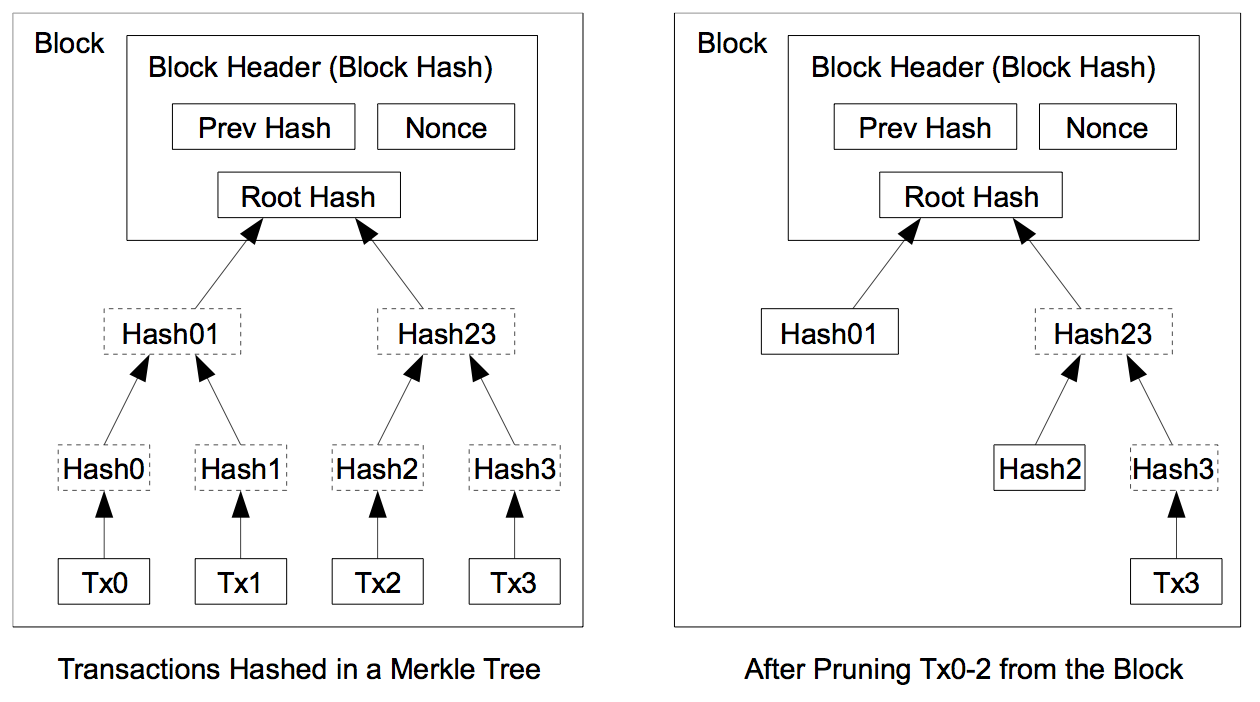
A block header with no transactions would be about 80 bytes. If we suppose blocks are generated every 10 minutes, 80 bytes * 6 * 24 * 365 = 4.2MB per year. With computer systems typically selling with 2GB of RAM as of 2008, and Moore’s Law predicting current growth of 1.2GB per year, storage should not be a problem even if the block headers must be kept in memory.8. Simplified Payment Verification
It is possible to verify payments without running a full network node. A user only needs to keep a copy of the block headers of the longest proof-of-work chain, which he can get by querying network nodes until he’s convinced he has the longest chain, and obtain the Merkle branch linking the transaction to the block it’s timestamped in. He can’t check the transaction for himself, but by linking it to a place in the chain, he can see that a network node has accepted it, and blocks added after it further confirm the network has accepted it.
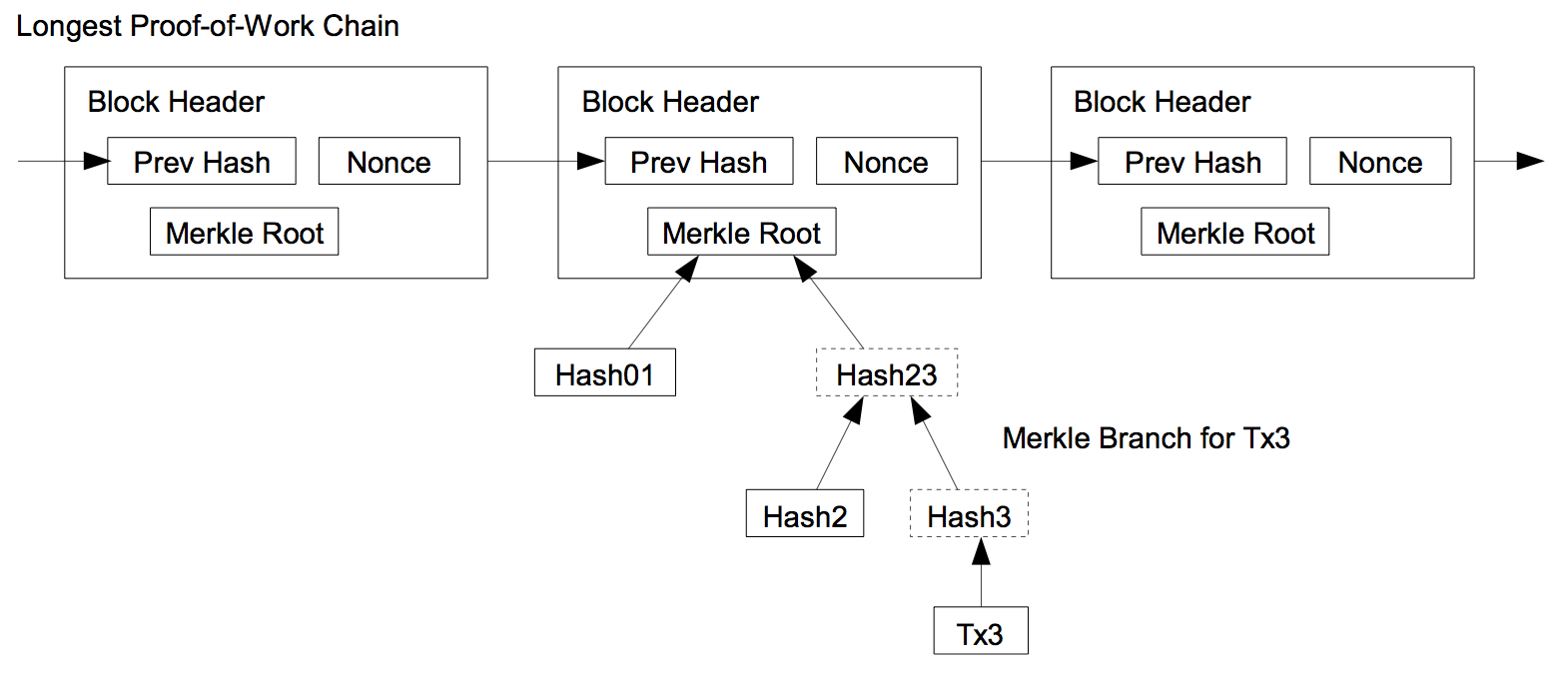
As such, the verification is reliable as long as honest nodes control the network, but is more vulnerable if the network is overpowered by an attacker. While network nodes can verify transactions for themselves, the simplified method can be fooled by an attacker’s fabricated transactions for as long as the attacker can continue to overpower the network. One strategy to protect against this would be to accept alerts from network nodes when they detect an invalid block, prompting the user’s software to download the full block and alerted transactions to confirm the inconsistency. Businesses that receive frequent payments will probably still want to run their own nodes for more independent security and quicker verification.9. Combining and Splitting Value
Although it would be possible to handle coins individually, it would be unwieldy to make a separate transaction for every cent in a transfer. To allow value to be split and combined, transactions contain multiple inputs and outputs. Normally there will be either a single input from a larger previous transaction or multiple inputs combining smaller amounts, and at most two outputs: one for the payment, and one returning the change, if any, back to the sender.
It should be noted that fan-out, where a transaction depends on several transactions, and those transactions depend on many more, is not a problem here. There is never the need to extract a complete standalone copy of a transaction’s history.10. Privacy
The traditional banking model achieves a level of privacy by limiting access to information to the parties involved and the trusted third party. The necessity to announce all transactions publicly precludes this method, but privacy can still be maintained by breaking the flow of information in another place: by keeping public keys anonymous. The public can see that someone is sending an amount to someone else, but without information linking the transaction to anyone. This is similar to the level of information released by stock exchanges, where the time and size of individual trades, the “tape”, is made public, but without telling who the parties were.
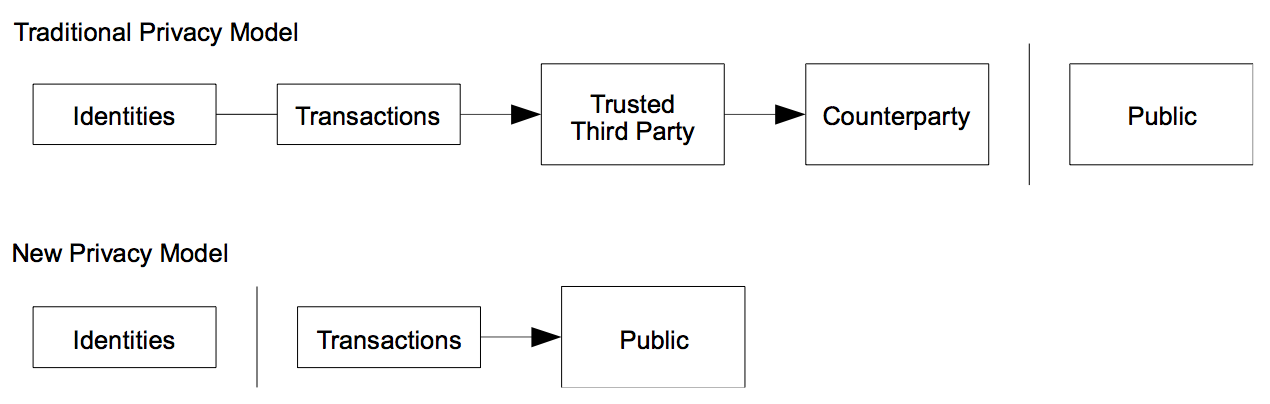
As an additional firewall, a new key pair should be used for each transaction to keep them from being linked to a common owner. Some linking is still unavoidable with multi-input transactions, which necessarily reveal that their inputs were owned by the same owner. The risk is that if the owner of a key is revealed, linking could reveal other transactions that belonged to the same owner.11. Calculations
We consider the scenario of an attacker trying to generate an alternate chain faster than the honest chain. Even if this is accomplished, it does not throw the system open to arbitrary changes, such as creating value out of thin air or taking money that never belonged to the attacker. Nodes are not going to accept an invalid transaction as payment, and honest nodes will never accept a block containing them. An attacker can only try to change one of his own transactions to take back money he recently spent.
The race between the honest chain and an attacker chain can be characterized as a Binomial Random Walk. The success event is the honest chain being extended by one block, increasing its lead by +1, and the failure event is the attacker’s chain being extended by one block, reducing the gap by -1.
The probability of an attacker catching up from a given deficit is analogous to a Gambler’s Ruin problem. Suppose a gambler with unlimited credit starts at a deficit and plays potentially an infinite number of trials to try to reach breakeven. We can calculate the probability he ever reaches breakeven, or that an attacker ever catches up with the honest chain, as follows [8]:
p = probability an honest node finds the next block
q = probability the attacker finds the next block
qz = probability the attacker will ever catch up from z blocks behind
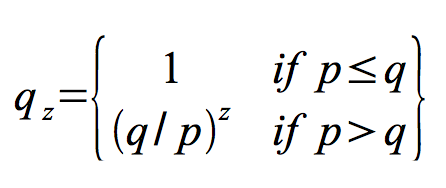
Given our assumption that p > q, the probability drops exponentially as the number of blocks the attacker has to catch up with increases. With the odds against him, if he doesn’t make a lucky lunge forward early on, his chances become vanishingly small as he falls further behind.
We now consider how long the recipient of a new transaction needs to wait before being sufficiently certain the sender can’t change the transaction. We assume the sender is an attacker who wants to make the recipient believe he paid him for a while, then switch it to pay back to himself after some time has passed. The receiver will be alerted when that happens, but the sender hopes it will be too late.
The receiver generates a new key pair and gives the public key to the sender shortly before signing. This prevents the sender from preparing a chain of blocks ahead of time by working on it continuously until he is lucky enough to get far enough ahead, then executing the transaction at that moment. Once the transaction is sent, the dishonest sender starts working in secret on a parallel chain containing an alternate version of his transaction.
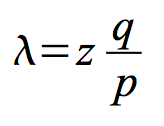
The recipient waits until the transaction has been added to a block and z blocks have been linked after it. He doesn’t know the exact amount of progress the attacker has made, but assuming the honest blocks took the average expected time per block, the attacker’s potential progress will be a Poisson distribution with expected value:
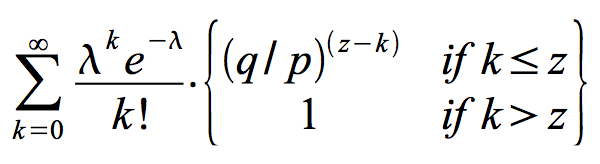
To get the probability the attacker could still catch up now, we multiply the Poisson density for each amount of progress he could have made by the probability he could catch up from that point:
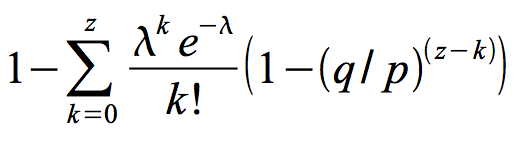
Rearranging to avoid summing the infinite tail of the distribution…
Converting to C code…#include <math.h> double AttackerSuccessProbability(double q, int z) {double p = 1.0 - q; double lambda = z * (q / p); double sum = 1.0; int i, k; for (k = 0; k <= z; k++) {double poisson = exp(-lambda); for (i = 1; i <= k; i++)poisson *= lambda / i; sum -= poisson * (1 - pow(q / p, z - k));}return sum;}Running some results, we can see the probability drop off exponentially with z.
q=0.1 z=0 P=1.0000000 z=1 P=0.2045873 z=2 P=0.0509779 z=3 P=0.0131722 z=4 P=0.0034552 z=5 P=0.0009137 z=6 P=0.0002428 z=7 P=0.0000647 z=8 P=0.0000173 z=9 P=0.0000046 z=10 P=0.0000012q=0.3 z=0 P=1.0000000 z=5 P=0.1773523 z=10 P=0.0416605 z=15 P=0.0101008 z=20 P=0.0024804 z=25 P=0.0006132 z=30 P=0.0001522 z=35 P=0.0000379 z=40 P=0.0000095 z=45 P=0.0000024 z=50 P=0.0000006Solving for P less than 0.1%…P < 0.001 q=0.10 z=5 q=0.15 z=8 q=0.20 z=11 q=0.25 z=15 q=0.30 z=24 q=0.35 z=41 q=0.40 z=89 q=0.45 z=34012. Conclusion
We have proposed a system for electronic transactions without relying on trust. We started with the usual framework of coins made from digital signatures, which provides strong control of ownership, but is incomplete without a way to prevent double-spending. To solve this, we proposed a peer-to-peer network using proof-of-work to record a public history of transactions that quickly becomes computationally impractical for an attacker to change if honest nodes control a majority of CPU power. The network is robust in its unstructured simplicity. Nodes work all at once with little coordination. They do not need to be identified, since messages are not routed to any particular place and only need to be delivered on a best effort basis. Nodes can leave and rejoin the network at will, accepting the proof-of-work chain as proof of what happened while they were gone. They vote with their CPU power, expressing their acceptance of valid blocks by working on extending them and rejecting invalid blocks by refusing to work on them. Any needed rules and incentives can be enforced with this consensus mechanism.
References
[1] W. Dai, “b-money,” http://www.weidai.com/bmoney.txt, 1998.
[2] H. Massias, X.S. Avila, and J.-J. Quisquater, “Design of a secure timestamping service with minimal trust requirements,” In 20th Symposium on Information Theory in the Benelux, May 1999.
[3] S. Haber, W.S. Stornetta, “How to time-stamp a digital document,” In Journal of Cryptology, vol 3, no 2, pages 99-111, 1991.
[4] D. Bayer, S. Haber, W.S. Stornetta, “Improving the efficiency and reliability of digital time-stamping,” In Sequences II: Methods in Communication, Security and Computer Science, pages 329-334, 1993.
[5] S. Haber, W.S. Stornetta, “Secure names for bit-strings,” In Proceedings of the 4th ACM Conference on Computer and Communications Security, pages 28-35, April 1997.
[6] A. Back, “Hashcash – a denial of service counter-measure,” http://www.hashcash.org/papers/hashcash.pdf, 2002.
[7] R.C. Merkle, “Protocols for public key cryptosystems,” In Proc. 1980 Symposium on Security and Privacy, IEEE Computer Society, pages 122-133, April 1980.
[8] W. Feller, “An introduction to probability theory and its applications,” 1957.
BigBlueButton录像文件太多,Ubuntu Server硬盘不够怎么办?
使用BigBlueButton时开启了录制功能,时间一久就发现空间不够用了,于是先用最基本的操作,删掉已外理过的录音文件来清理出空间:
1. 清理Logsudo bbb-conf –clean2. 删除旧的录像、文档、/etc/cron.daily/bigbluebutton删除 `exit 0` 行来启用自动清理清理项有:find /var/bigbluebutton -maxdepth 1 -type d -name “*-*” -mtime +11 -exec rm -r ‘{}’ \;find /usr/share/red5/webapps/video/streams -name “*.flv” -mtime +1 -exec rm ‘{}’ \;find /var/bigbluebutton/deskshare -name “*.flv” -mtime +1 -exec rm ‘{}’ \;find /var/freeswitch/meetings -name “*.wav” -mtime +1 -exec rm ‘{}’ \;3. 删除已处理过的wav文件sudo find /var/bigbluebutton/recording/process -name “*.wav” -exec rm ‘{}’ \;
录像与回放功能目录结构
/usr/local/bigbluebutton/ └── core ├── Gemfile ├── Gemfile.lock ├── lib │ ├── recordandplayback │ │ ├── audio_archiver.rb │ │ ├── deskshare_archiver.rb │ │ ├── events_archiver.rb │ │ ├── generators │ │ │ ├── audio_processor.rb │ │ │ ├── audio.rb │ │ │ ├── events.rb │ │ │ ├── matterhorn_processor.rb │ │ │ ├── presentation.rb │ │ │ └── video.rb │ │ ├── presentation_archiver.rb │ │ └── video_archiver.rb │ └── recordandplayback.rb └── scripts ├── archive │ └── archive.rb ├── bbb-rap.sh ├── bigbluebutton.yml ├── cleanup.rb ├── process │ ├── README │ └── slides.rb ├── publish │ ├── README │ └── slides.rb ├── rap-worker.rb └── slides.yml最终录像回放存放目录
- /var/bigbluebutton/published/slides/<meeting-id>
修改录像与回放目录:把原有的录像路径下所有文件与目录拷到目标路径,如/mnt下sudo cp -a /var/bigbluebutton /mnt/则新的录像与回放目录为:/mnt/bigbluebuttonsudo vi /usr/local/bigbluebutton/core/scripts/slides.yml
修改其中的publish_dirsudo vi /usr/local/bigbluebutton/core/scripts/bigbluebutton.yml修改其中的recording_dir published_dir raw_deskshare_src raw_presentation_srcsudo vi /usr/local/bigbluebutton/core/scripts/cleanup.rb修改其中的PUBLISHED_DIR UNPUBLISHED_DIR RECORDING_DIRsudo vi /var/lib/tomcat6/webapps/bigbluebutton/WEB-INF/classes/bigbluebutton.properties
修改其中的presentationDir BLANK_SLIDE BLANK_THUMBNAIL recordStatusDir publishedDir unpublishedDir使用下面这条命令前先把地址修改为想要修改的地址,以便网络用户有权限访问该位置的内容sudo chown -R tomcat6:tomcat6 /mnt/bigbluebutton/playback/sudo vi /etc/bigbluebutton/nginx/slides.nginx修改其中的地址sudo chown tomcat6 /mnt/bigbluebutton修改目录所有者sudo bbb-conf –clean
- 把 /var/bigbluebutton目录内的文件移动到别处
- 新增一块硬盘挂载到/var/bigbluebutton目录
- 用ls -ld /var/bigbluebutton查看一下目录权限,所有者是否为tomcat6
- 如果不是则修改为tomcat6
- 把移到别处的文件拷回/var/bigbluebutton下
- 在sudo vi /etc/fstab中新建条目以便每次重启时自动加载
附上挂新硬盘的方法:
查看移动硬盘
sudo fdisk -l
挂载
sudo mount -t ext4 /dev/sdb1 /var/bigbluebutton
注:如果是fat32格式的则用-t vfat参数,如果是ext3格式的则用-t ext3参数,/dev/sdb1改为你要挂载的硬盘的实际名称
设置重启后自动挂载
sudo vi /etc/fstab
在该文件中添加:
/dev/sdb1 /var/bigbluebutton ext4 defaults 0 0
由于BigBlueButton当前版本对于录像的存储、发布等功能还是非常不完善,只能先这样处理了。
当硬盘再次满了的时候还会面临新的问题。再加一块的话要么加一块更大的硬盘,把原有的录像文件复制到新的硬盘上;要么就制定一个规则,把超过一定时间的录像文件删掉,腾出新的空间来用。
凤凰网微访谈:赵金海
今年前半年接受了一次凤凰网教育频道的访谈,信口开河,讲了讲对于英语学习、教学等的一些看法,不是学术讲座,难免有不严谨的地方,不过最起码是我最真实的感性认识。转到自己博客上,收藏一下。
原文链接:http://edu.ifeng.com/yurenzhe/special/zhaojinhai/
视频:
中国的外语教学落后西方100多年
凤凰网教育:各位网友大家好,欢迎来到凤凰网教育频道为您打造的视频访谈《育人者》节目。本期访谈我们专程为大家邀请到了2008年北京奥运会志愿者外语培训教学总监、教材主编,巴别鱼国际教育的校长赵金海老师,我们请赵老师和我们广大凤凰网的网友打个招呼。
赵金海:大家好。
凤凰网教育:赵老师好。我们今天主要聊的是关于外语学习的热门话题。我们知道随着时间的发展,中国越来越OPEN了,对外语的需求也特别大,但是我们发现国内的应试教育出来的很多学生们在说外语方面有很多的这个误区和弊病。
我本人从小学就已经接触到外语了,但是到了真正开始说的时候,还是说不出来。
赵金海:对,就跟上学一样,在学校学了那么多年,一到社会发现什么都不一样了。 Continue reading “凤凰网微访谈:赵金海”
开始玩天文望远镜
一直以来都特别想买天文望远镜,但在北京空气质量这么差,总是想等将来离开北京再说。可是到春节前的时候,实在等不了了,即使看不了太多东西,总比不看好。于是买了一架入门级的先玩玩。
点击图片可以看大图
Temper Run秘技
别急,标题没有写错单词。
好多人玩Temple Run,就是一个人被大猩猩追着跑,看你能跑多远。路其实分左、中、右三条道,途中会遇到很多障碍和岔道,需要灵敏地躲过。这让我不仅想到人生的道路,这三条道可以是“自卑←自信→自负”。人一生中其实就在这三条道之间不断地切换。暂且把人生这个游戏叫做Temper Run吧,一方面Temper与Temple可以押点韵,另一方面你有什么样的心态就会呈现出相应的脾气,所以把人生的游戏叫做Temper Run还是可以说得过去的。
“自卑←自信→自负”这三条道每个人都在跑,只是有些人貌似在其中一条道上跑得多一些,我们就自然而然地认为他们是什么样的人。其实我们都知道,自信的人经常有感到自卑的时候,自卑的人很容易变得自负,而自负的人其实很可能就是内心深处的自卑导致的。
这三个词在我们的语言中有明显的偏向性,只有自信是褒义词。这说明自信是在人类社会中生存的重要品质。这种偏向实际是理想化的,因为没有人是绝对自信的,同样没有绝对自卑或自负的人。很多人认为(或者潜意识中认为)自信的人可以拥有美好的人生,正是这种观念让人不得自由,要有意无意地去维护这种信念。维护的结果就是用力过猛而成为自负,伤到自己后又成为自卑,偶尔跑到自信的道上享受了一下后又要回到两边徘徊。其实根本不是美好的人生,这一点只有自己最清楚。
要真正活得自在就需要中立地看待这三种心态。如果要想中立地看待的话,就需要把有偏向性的名称换掉。这三种心态说到底其实都是对自己的认可与否(无论如何,人的一生一定是以自我为中心的,无我的时候就要成佛了)。根据认可程度的深浅大体划分为三份。所以可以把这三种心态的名字改为“State A、State B、State C”,其中State A是指对自己不认可,State B是指对自己认可,State C是指对自己过分认可。我们需要State A来对自己分析、反省,需要State B让我们大步前进,需要State C让我们勇于冒险。不要偏爱任何一种状态。一味地努力维护其中一种状态会导致盲目,看不清自己到底是在哪条道上,进而导致自己和他人的痛苦。
我们拥有一个奇妙的大脑,它会自动在恰当的时候切换状态,把你带到相应的道上,你只需要在当前道上好好跑就可以。很多时候我们冷静下来都会发现自己内心深处其实知道当下应当做什么,可是就是不去那样做,这正是在为维护某一种状态而跟自己的大脑做对抗(执著、颠倒)。如果不及时停止这种执著,等到造成无法挽回的后果时就后悔莫及了。所以Temper Run的秘技很简单,就是让内心深处的那个力量(那其实才是真正的你)为你换道,三条道并行,不偏不倚。
Temple Run我没怎么玩过,但Temper Run每个人都在玩,希望这个秘技能帮到你。